Single-Sign-On (SSO)
Add-on to your Enterprise planThis functionality is available as an additional add-on for your Enterprise plan. For detailed questions, please customer success teamIf you want to use the Single-Sign-On authentication method, please contact our team to get the necessary custom information for your individual integration.
If your Usersnap account is SSO-enabled, you can have your employees authenticated with your internal authentication methods and security measurements. Additionally, you can add external team members with email and passwords as their login methods.
This allows you to add internal and external team members to your projects.
If you have any questions, please do not hesitate to contact us.
Okta (SAML 2.0)
Following this guide:
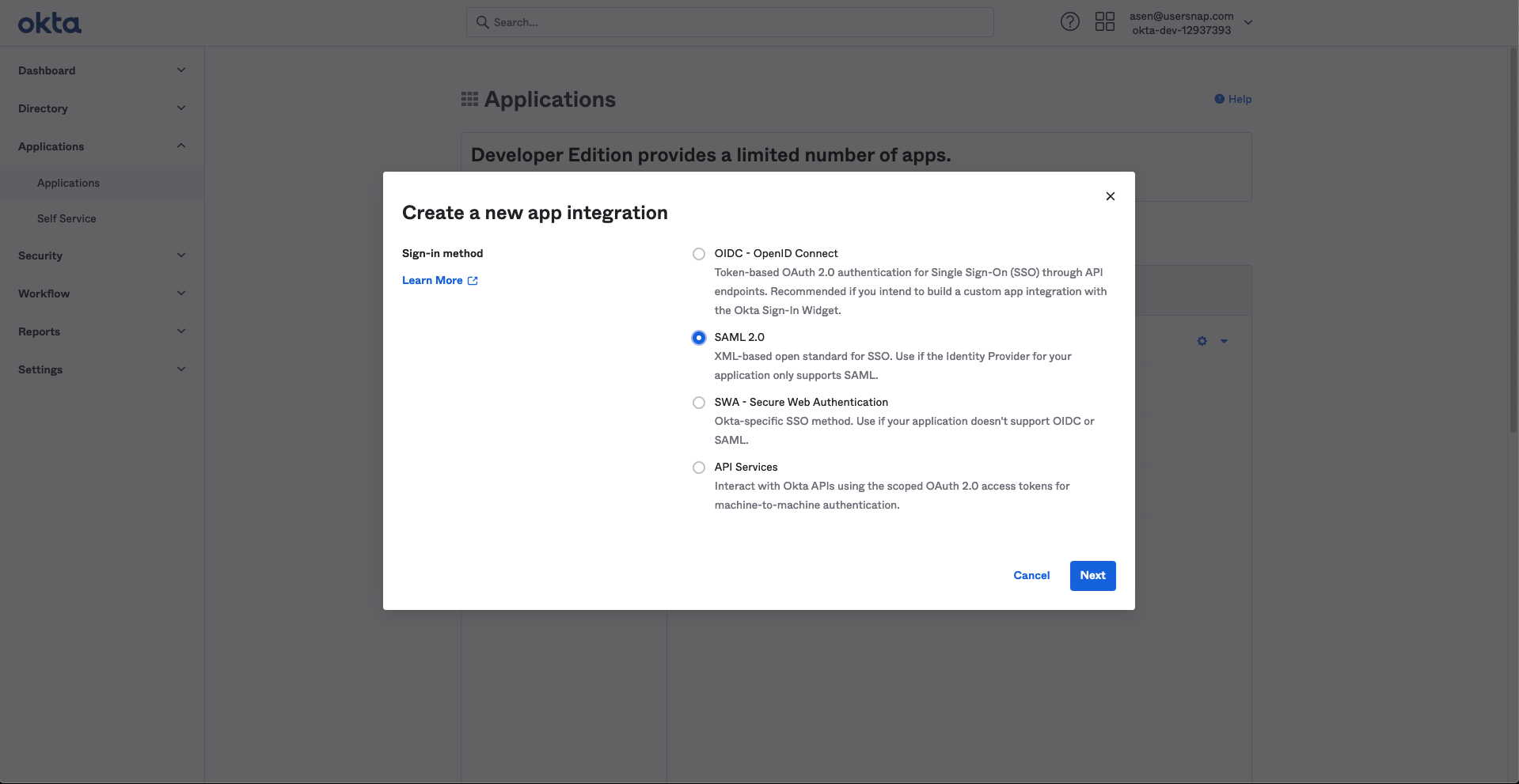
- Create a new SAML Okta application integration.
- In the settings, configure the fields as follows:
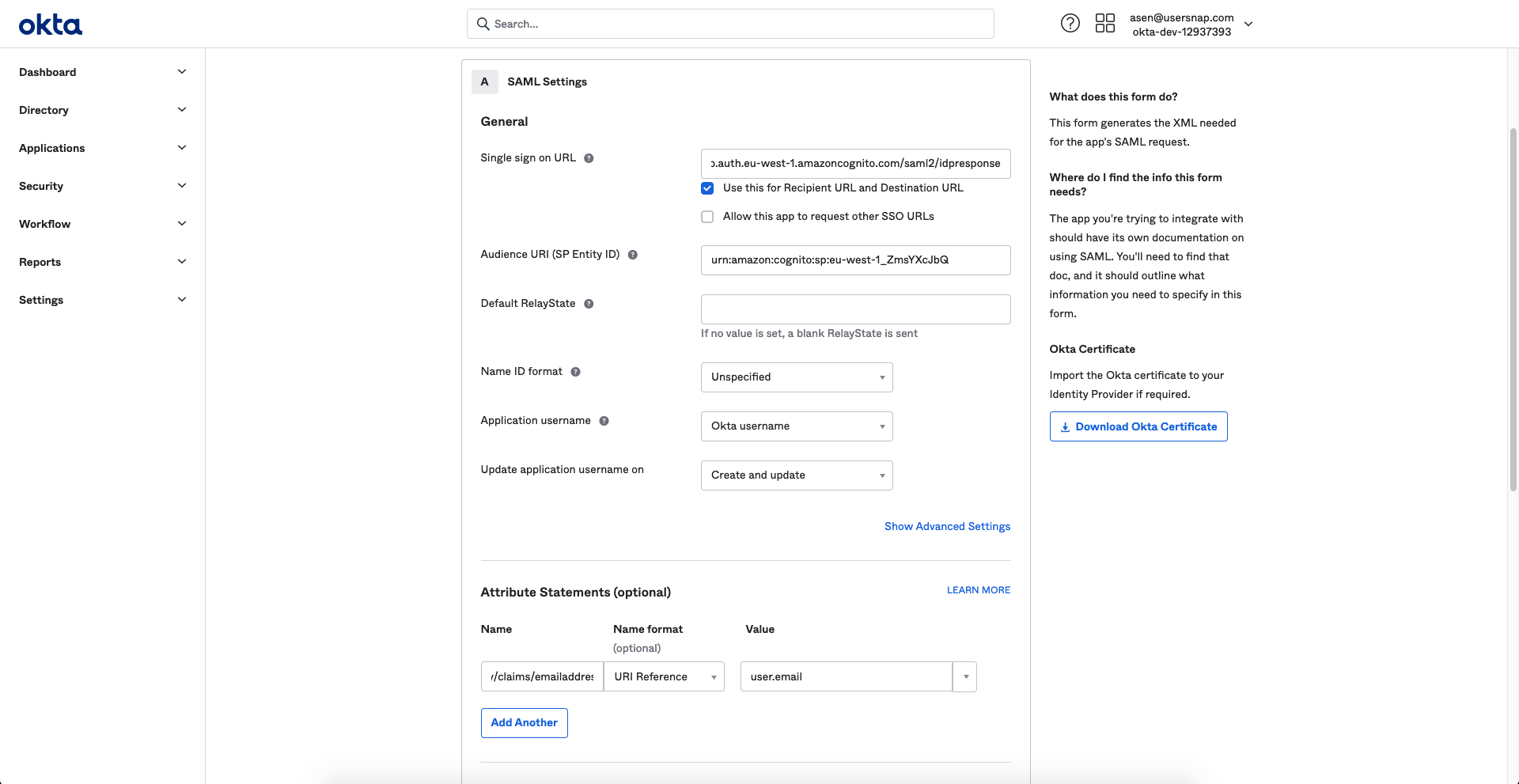
- SSO URL - this URL will be provided by Usersnap. It will be similar to this one: https://us-XXXXX-basic-setup.auth.eu-west-1.amazoncognito.com/saml2/idpresponse
- Audience URI - this URI will be provided by Usersnap. It will be similar to urn:amazon:cognito:sp:eu-west-1_XXXXXXXX
- Attribute statements:
-- Name: emailaddress
-- Value: user.email
-- Name: name
-- Value: user.firstName
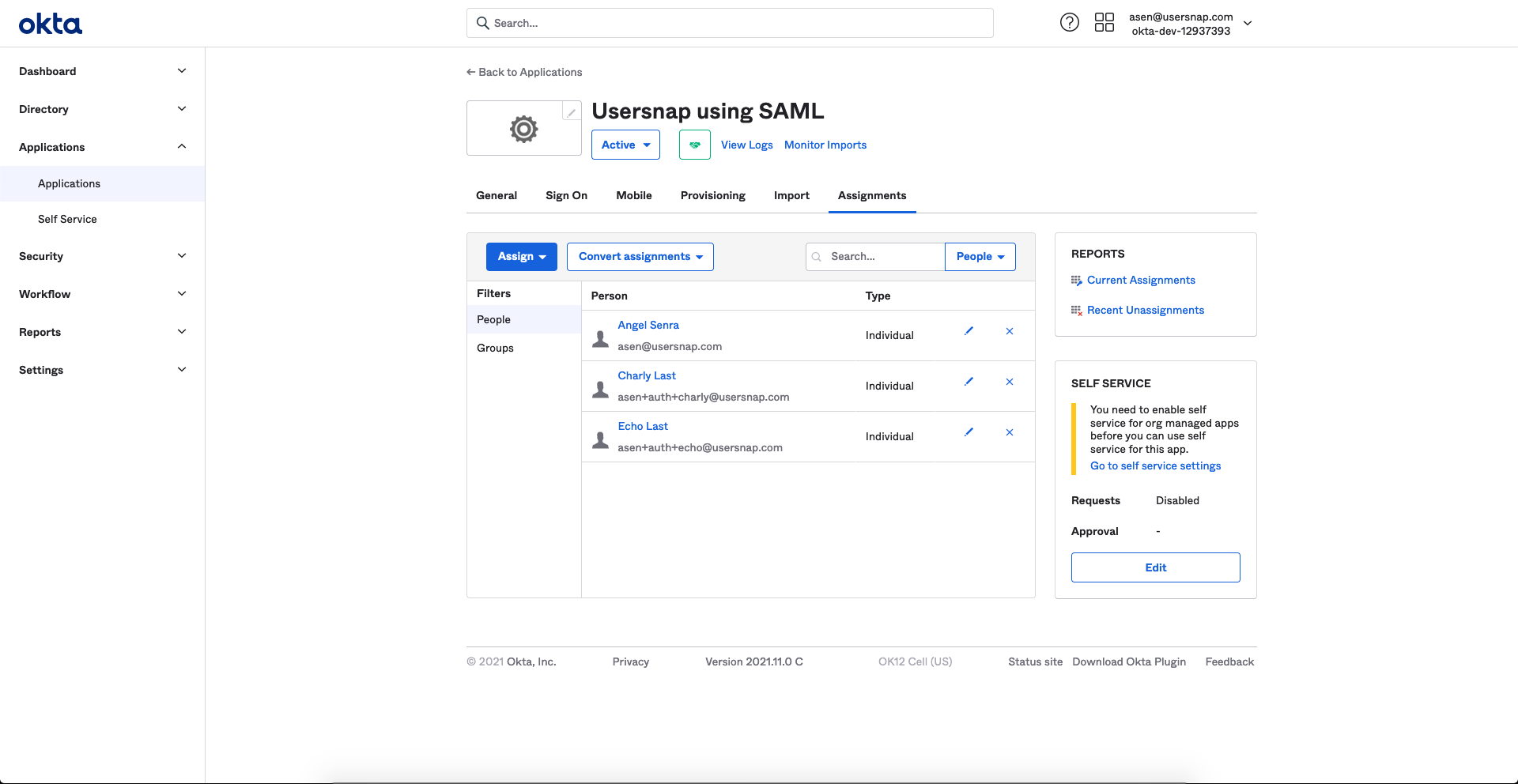
- After creating the app, assign some users that you want to be able to log in to Usersnap.
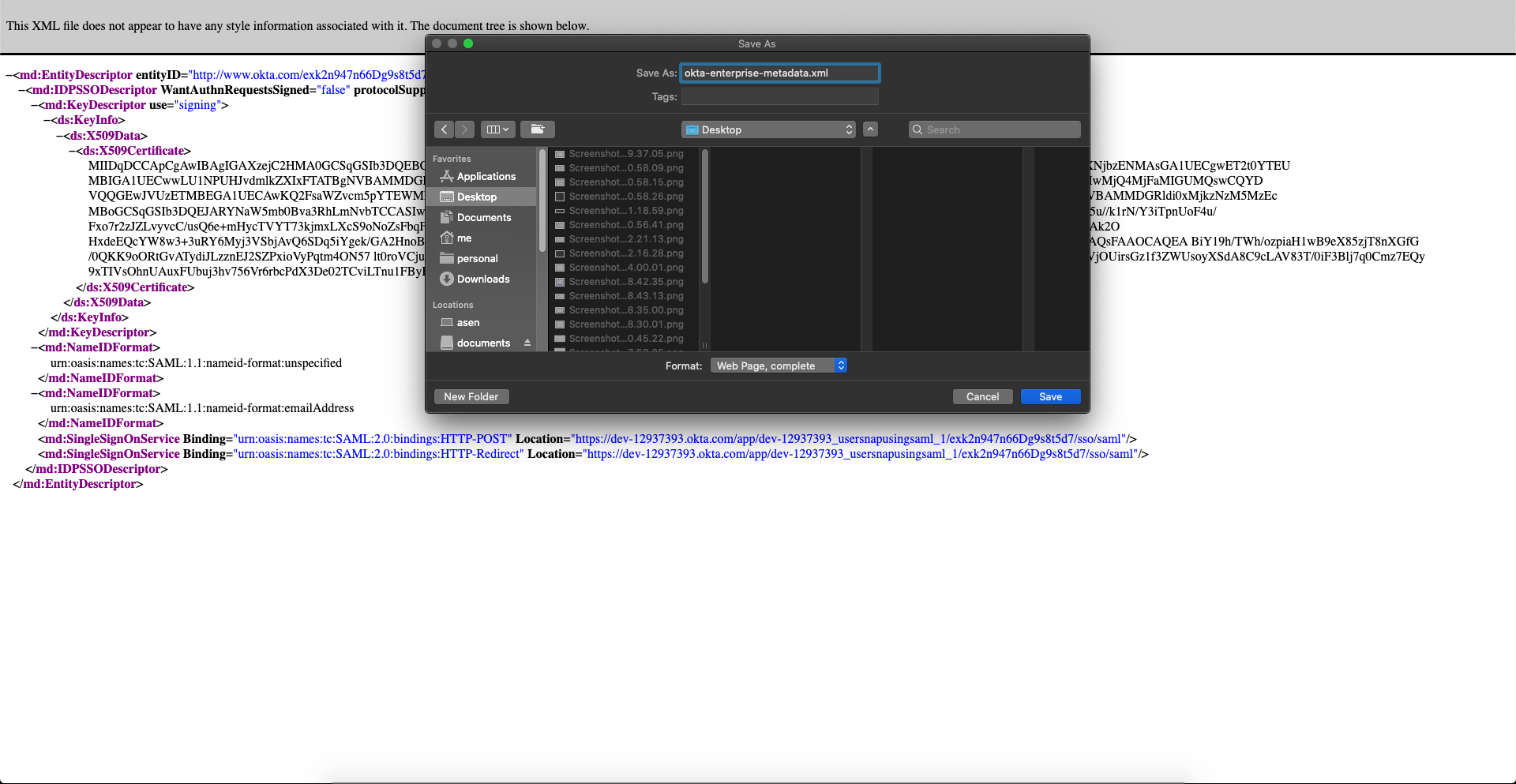
- Finally, open the Identity Provider metadata.
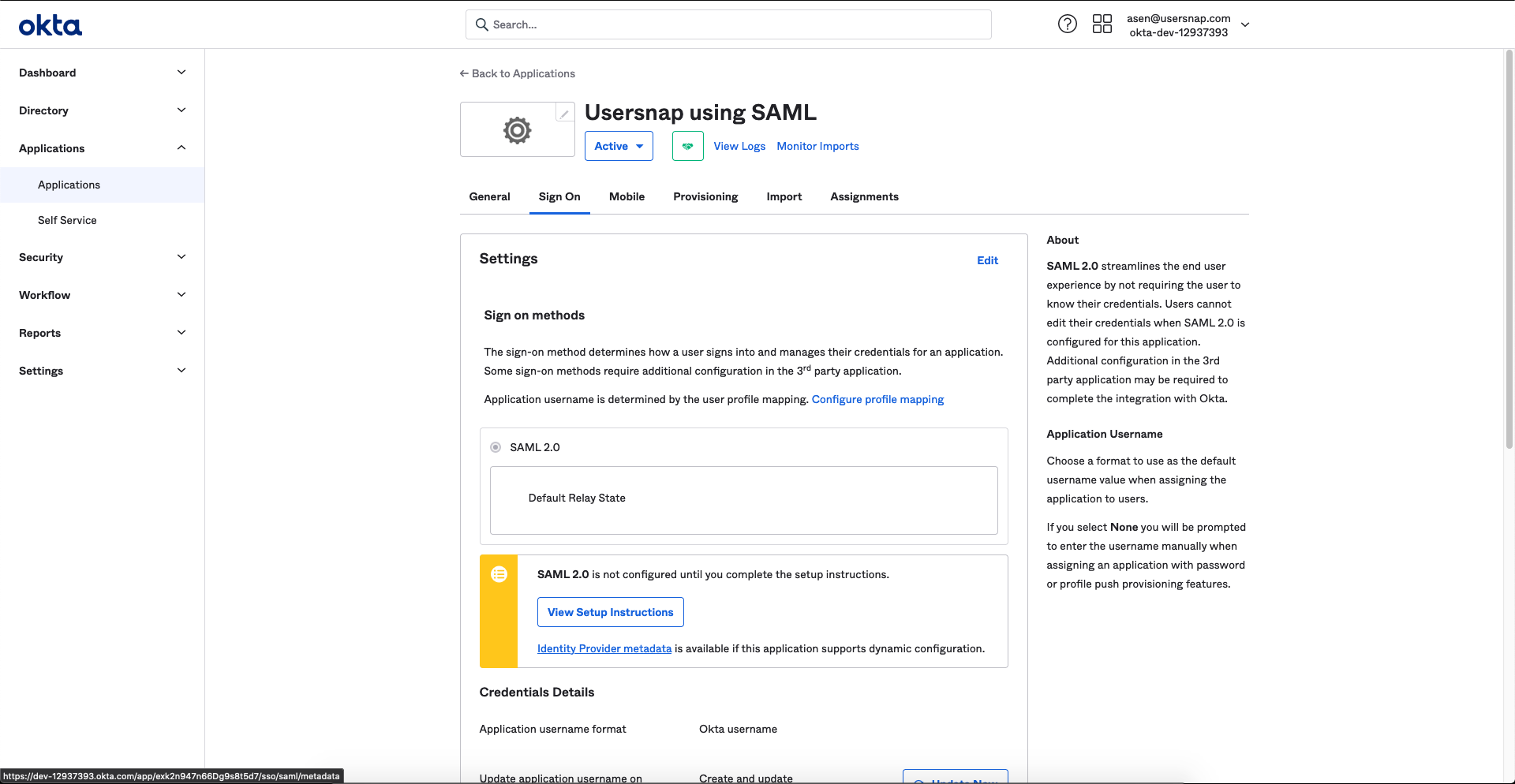
- And download the XML-file. You will need to send this file to Usersnap.
Azure Dev Ops SSO integrationAs Azure Dev Ops SSO functions in the same fashion as Okta (SAML2), please take the above mentioned as reference for its set-up.
Okta (OIDC - OpenID Connect)
Following this guide
- Create a new OIDC Okta application integration.
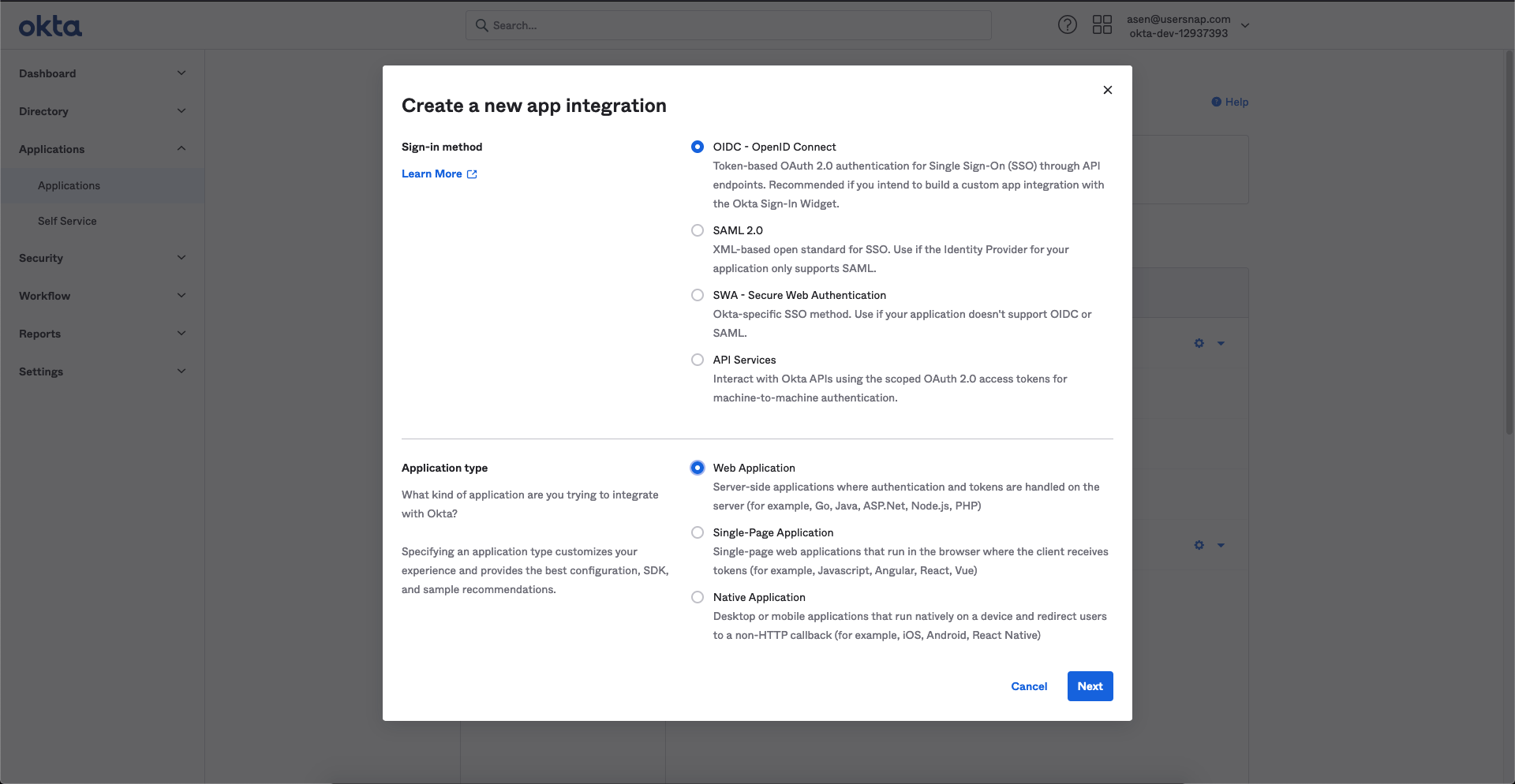
- In the settings - Configure the fields as follows:
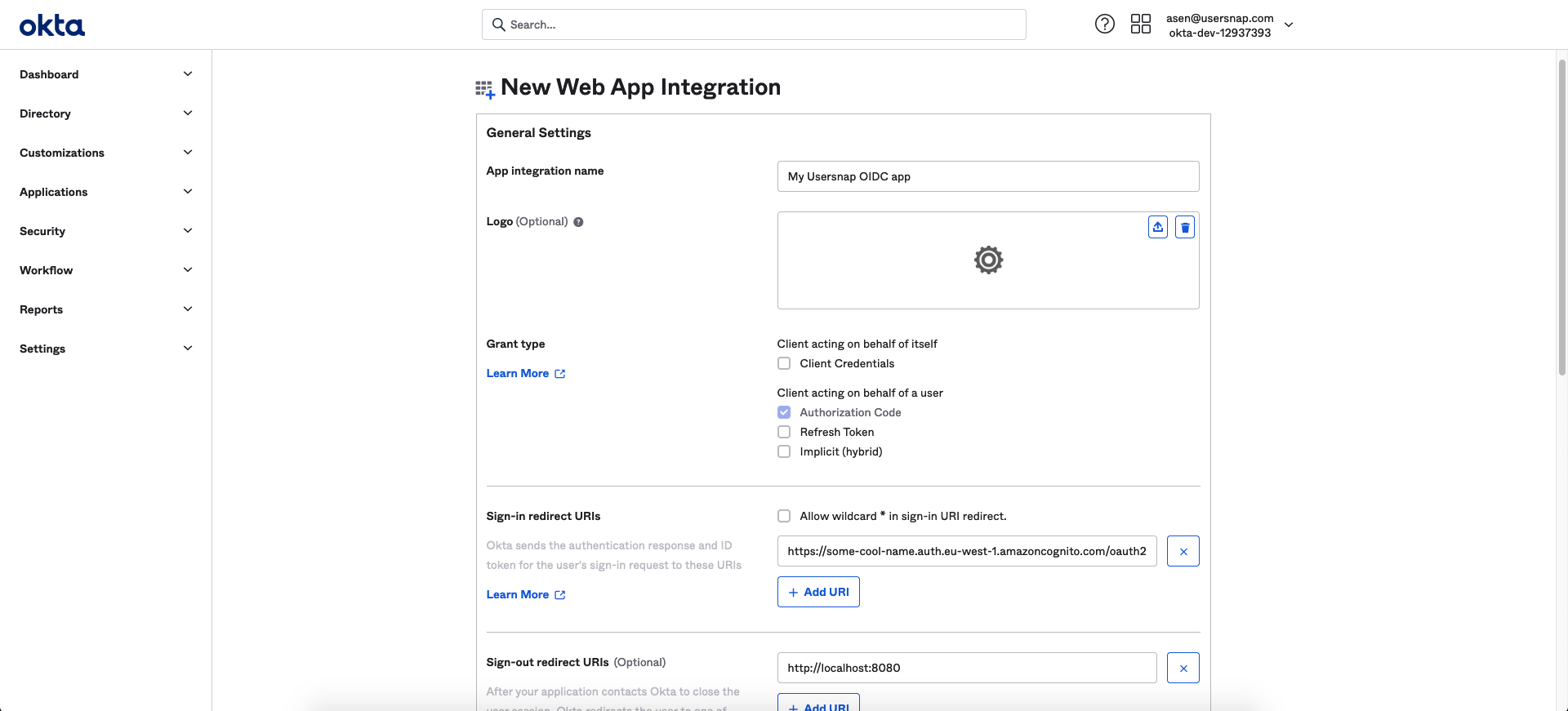
Sign-in redirect URI: This will be provided by Usersnap. It will look similar to this one https://us-XXXX-basic-setup.auth.eu-west-1.amazoncognito.com/oauth2/idpresponse
- Copy the Client ID and Secret. You will need to send this to Usersnap.
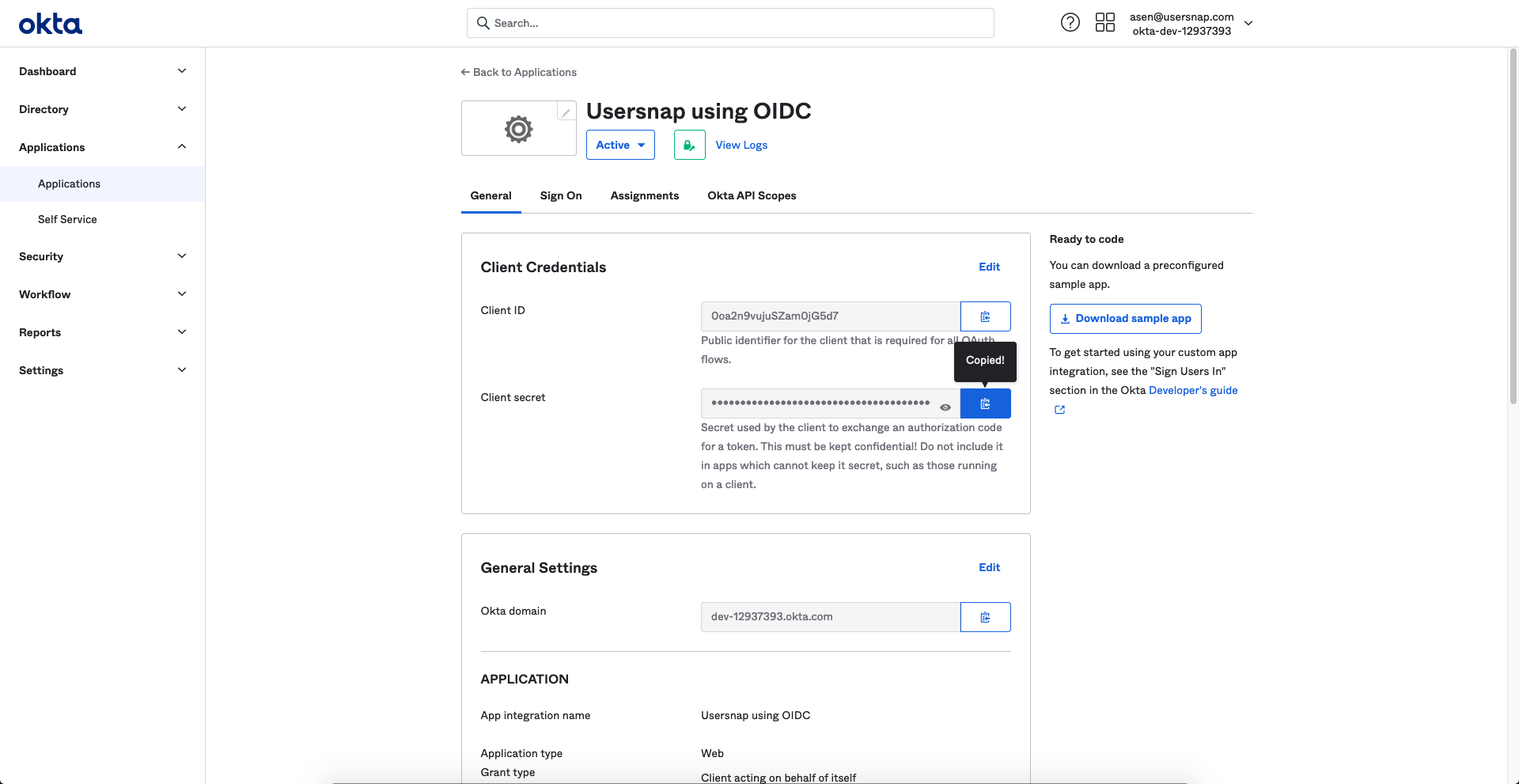
- Copy the issuer URL.
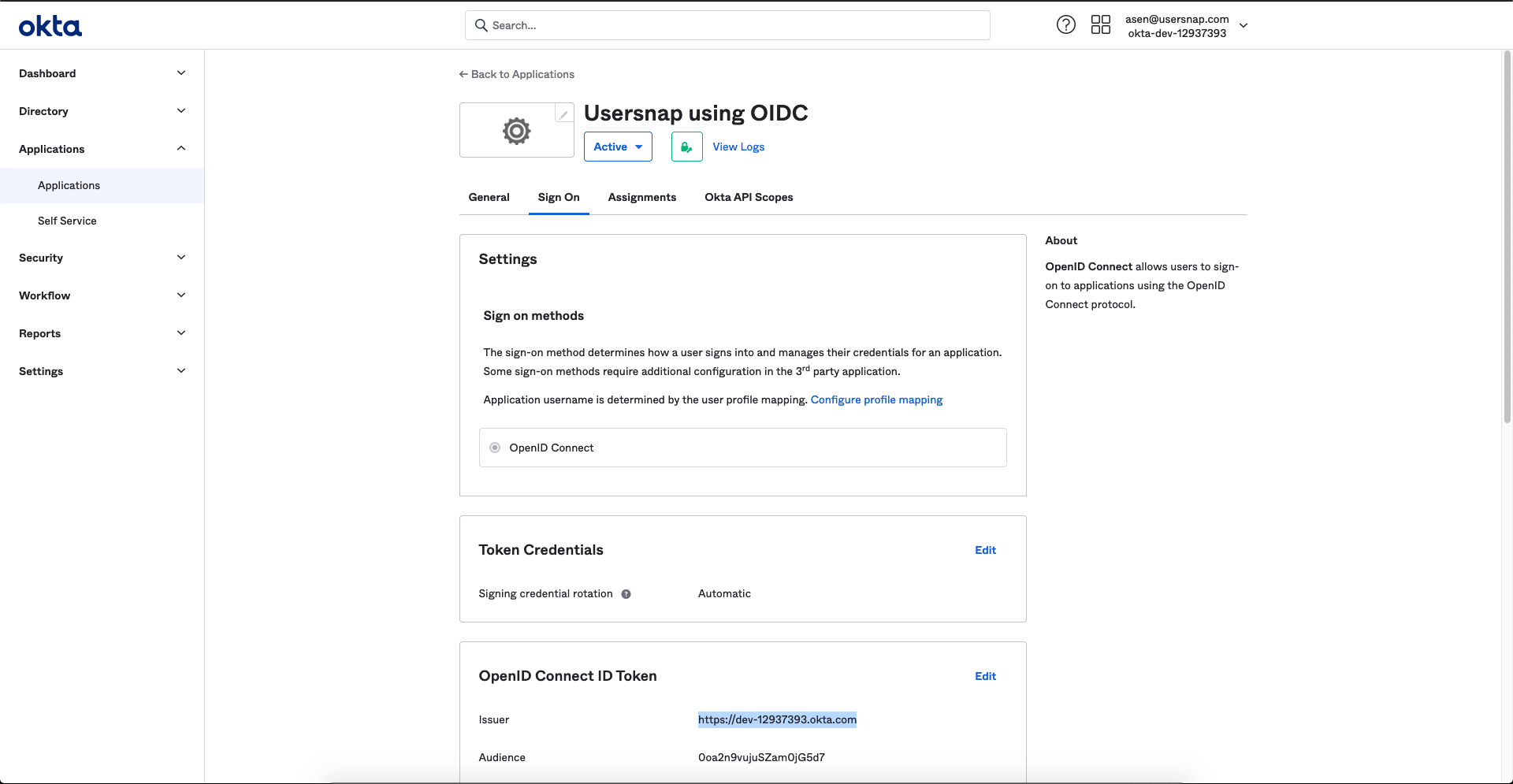
- Please send the issuer URL to Usersnap.
Set the team members' authentication method
You now have the flexibility to customize the authentication method for each team member. This means you can choose the best method for each individual to sign in with.
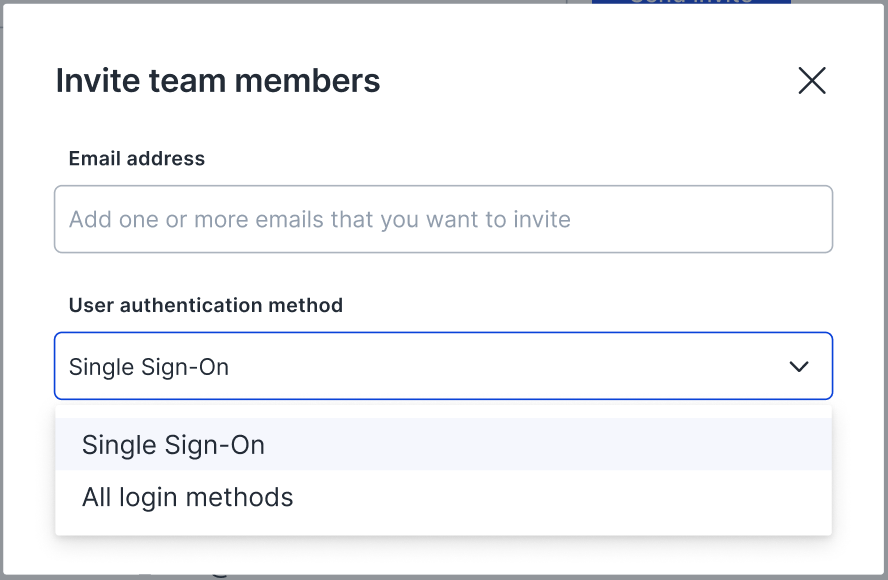
In addition, you can easily set a default authentication method for your team by visiting the "Manage team" page within the Usersnap dashboard.

Enforcing the Single Sign-On method is also possible. Enforcing SSO means that the system will not allow access to any of its applications or services without the user first logging in through the SSO system. This can increase security and convenience for users.
Please note that...
- These modifications can only be carried out by admins.
- When SSO is enabled, the ability to use 2-Factor Authentication in individual user accounts will be disabled.
Updated about 1 year ago
